Event Store blog
-
Last week, the Event Store team attended QCon London, one of the largest international software development conferences. Here's...
-
We’re delighted to announce that we’ve been named a Finalist in the British Data Awards 2024.
-
Last week, the Event Store team had the pleasure of attending Explore DDD 2024, a triumphant return for the conference in the US.
-
Event Store is excited to be joining this year's QCon London as a gold sponsor, taking place from 8th - 10th April.
-
Excitement is in the air as we gear up for Explore DDD next week! This event brings together a diverse international community of...
-
Today, we are excited to announce that the EventStoreDB 24.2 Release is here. This release is a significant update that...
-
The official EventStoreDB security release for versions 23.10, 22.10, 21.10, and 20.10 is now available. The versions in this...
-
Event sourcing is a software design pattern where the state of your application is determined by a sequence of immutable events,...
-
Command Query Responsibility Segregation (CQRS) is a design pattern that has gained popularity for its ability to enhance the...
-
With EventStoreDB, there is no need to get rid of everything you’ve built in PostgreSQL. You can use EventStoreDB for your...
-
In the ever-evolving landscape of software architecture, one paradigm stands out for its ability to capture the essence of...
-
Explore DDD, the conference where software professionals come together to discuss advanced Domain Driven Design topics and its...
-
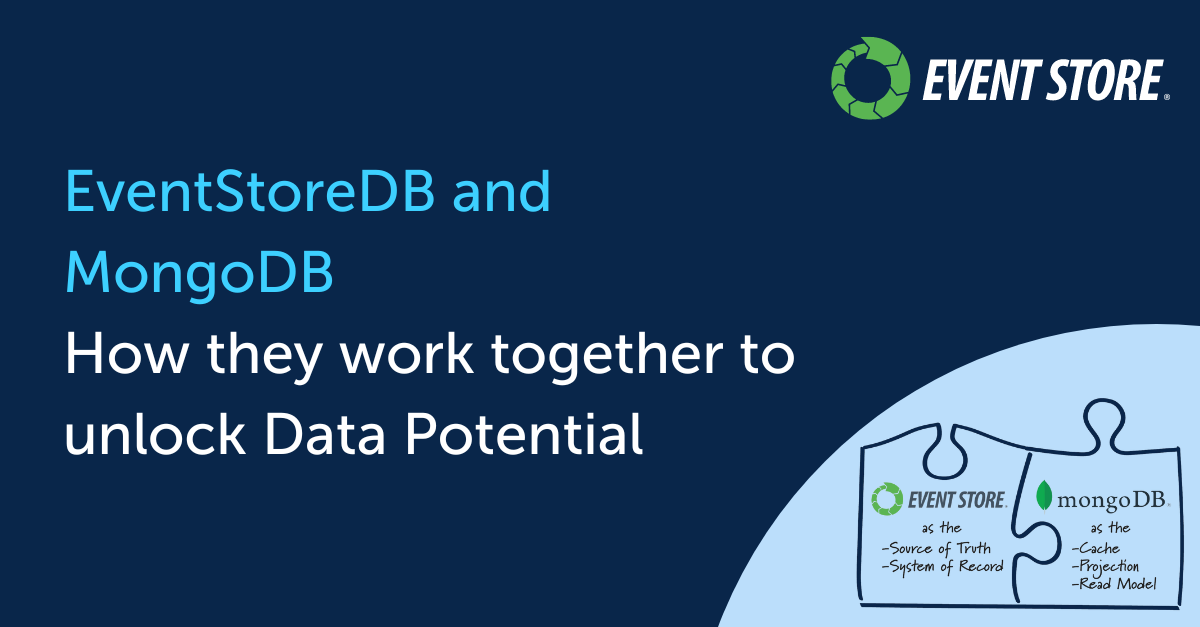
What if you could scale and distribute data freely, without forming a tightly coupled mess? And what would you say if we told you...
-
-
-
Introducing the new Python client for EventStoreDB – a fusion of two powerful technologies that promises to transform the way you...
-
-
-
In EventStoreDB v23.6 we made it much easier to collect and process key metrics from the server. This feature is now supported in...
-
EventStoreDB 23.10.0 builds on the security changes introduced in 23.6.0. The security highlights in this version are: Allow...